Before diving into this topic, if you need a basic understanding of PKI and where it is used, please read my previous two posts about PKI. Public Key Infrastructure or PKI in short, is a set of policies, technologies and procedures which creates a system of trust that can ensure the security of information systems. PKI works on three key areas of security. Authentication, Integrity and Non-repudiation.
- Authentication: This ensures that information accessed by only those people who are actually intended to access that information.
- Integrity: This area ensures that the information presented is correct and not modified in transit or elsewhere.
- Non-repudiation: It is a form of contract that ensures the parties involved in an information exchange or transaction can not deny that they have made that transaction.
From a technological point of view, PKI provides this security through asymmetric cryptography. Digital Signature and Encryption techniques provide the security of the information. Digital Certificates ensure the identity of the parties involved. Now, the question is, how do we design this system of trust? Before answering that, let’s get familiar with some entities those are involved in a PKI.
- Registration Authority (RA): A registration authority is responsible for verifying the identity of anyone who is willing to get a digital certificate. A RA can be a private organization or a government entity depending on the policy of the governing authority. RA provides the verification service to a CA which in turn issues the digital certificate.
- Certificate Authority (CA): A certificate authority is responsible for issuing digital certificates. CA ensures the identity of the individual taking the digital certificate through RA.
- Validation Authority (VA): A validation authority checks the validity of a digital certificate issued by a CA.
RA, CA and VA can be the same organization or can be separate organizations collaborating with each other. However, these entities are essential in a Public Key Infrastructure.
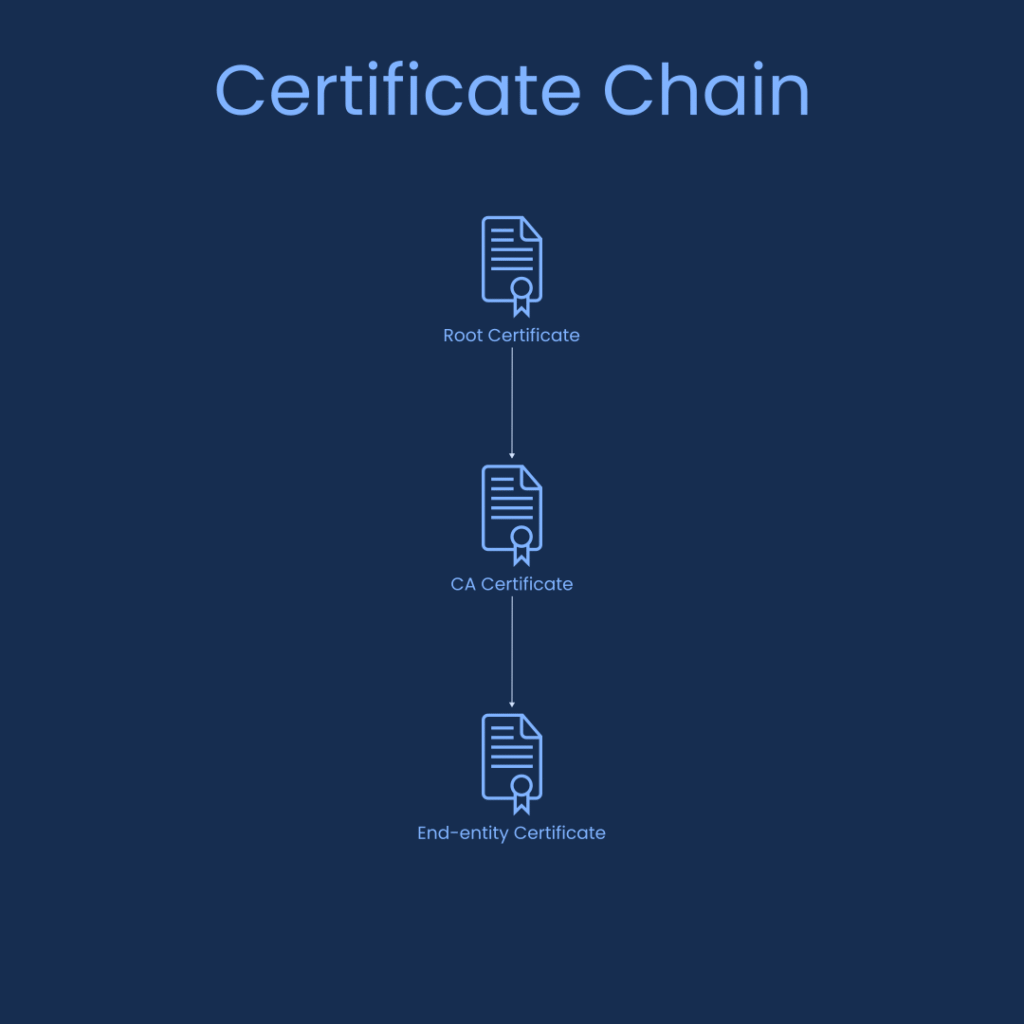
In order to establish a trusted system there needs to be a trusted body who governs the system and ensures that all the procedures are performed according to well defined policies. Often, this trusted body is a government organization. The government organization issues a root certificate. Then, the government issues CA certificates which are signed by the root certificate. The CAs are then responsible for issuing certificates to end users according to their specific requirements. This is called bridge certification method. This method establishes a chain of trust. Everyone involved in an information transaction trusts the root certificate. So, they also trust any certificate that is chained to the root certificate.
There is another way where the government only acts as a mediator. Every CA maintains their own root certificate. However, the government can ensure that every CA trusts the root certificates of other CAs. This method creates a mesh of trust. Hence, it is called mesh certification.
Now, let’s talk about policies. We have discussed that PKI provides security through asymmetric cryptography which comprises of private and public key pairs. The CAs are responsible for the generation, storage and destruction of these key pairs. As the key pairs are bound to the identity of an individual and essentially represents them in a digital environment, it is crucial that the key pairs are handled in an absolute secure way. This is where the policies come into play. CAs make sure they explicitly declare how they are handling the generation, storage and destruction of the key pairs in their Certificate Policy (CP) and issue a Certificate Policy Statement (CPS) that contains the CP. The CP may also contain pricing policy of a CA.
In order to securely handle the key pairs, the CAs often use Hardware Security Module (HSM) which is a cryptographic device specifically designed to maintain the lifecycle of a key pair and ensures the private key never leaves the HSM. A HSM is used in a server. However, there are other methods where the private key might be stored in a portable USB device or a smart card. There are systems which use the smartphone as a security device as most smartphones these days come with a security chip built-in.
So, let’s answer the question we raised at the beginning. In order to design a PKI, we need a RA who will verify the identity of a customer. This verification result is then sent to a CA who issues a Digital Certificate to the customer. The CA is monitored by a trusted body, often, a government entity. CAs define operational policies in CP and publishes them through a CPS. PKI uses private-public key pair and the private key is securely stored in a HSM in a server or an external security device belonging to the customer. Finally, any relying party who accepts Digital Signatures can verify the Digital Certificate of the signature through a VA.




